Maritime Cyber Security
We support the maritime & offshore operators in securing their assets.
Cywake interconnects the maritime, digital and risk management cultures.
We are seafarers, computer engineers and experts on Maritime & Offshore industry.
We combine marine operations, marine engineering and information systems backgrounds.
Cyber risk management
A global approach is the key to success.
It shall encompass:
- The human factor
- The organisational set-up
- The IT/OT shipboard systems
Cyber risk management is a continuous improvement process of audits, architectrure mapping, incidents recording, technology watch, regulatory watch, threat assessment, risk evaluation, mitigation measures and trainings with the challenge to always keep operational flexibility.
While the cyber security is perceived as a technology matter, it is massively relying on human behaviour. Not less than 80% of cyber attacks comes from employee’s mistakes.
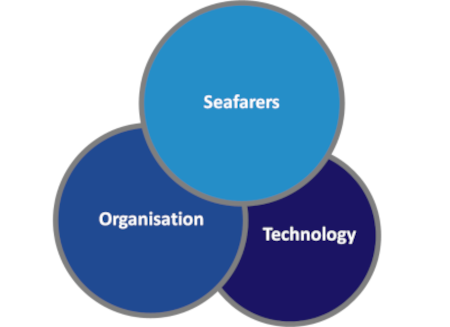
An effective cyber security system involve the company organisation and must be integrated in the existing safety/security management systems.
Cyber security is of course also a matter of advance technology, physical and logical barriers, which need innovation to stay up to date with threats.
Finally, regarding the multiple regulations we currently start to see in the industry, it also can be seen as a lever for business differentiation.

Cyber Threat
Ransomware groups
Hacktivists
Cyber-terrorists
State driven organization
Angry employee
Competitors

Impacts
Safety risks for assets and seafarers
Direct Costs:
Operational Downtime – Data losses – Class losses
Indirect Costs:
Trademark deterioration – Loss of Business
Regulation
IMO MSC 428(98) – ISM
ANSSI & NIST Recommendations
Flag state guidance’s
Class (cyber resilience notations)
Insurances cyber clauses, exclusions
Clients (chartering contracts)

Maritime Cybersecurity overall answer to reduce your cyber risks
Reduce your Cyber Risks
- Improve your operational resilience
- Protect your seafarers
- Secure your assets and data
- Comply with class, insurances and charters-party requirements
At Cywake, we apply a risk-based approach inherited from our Oil&Gas offshore culture.
We know marine operations, shipmanagement, technical management.
We have driven changes in organisations, we know how to take the complexity of the human factor into account and master the regulatory stakes.
We keep on the leading edge of the hacking technologies and technics and develop our own ethical hacking platform.
Our Services
Maintenance in Security Condition
- Mapping of critical shipboard systems (OT/IT)
- Analysis of vulnerabilities and threats
- Dynamic assessment of the risk
- Pentesting focused on vessels
- Operational & Technical mitigation plan
Compliance & Regulation
- Design, writing and implementation of policies, process & guides
- IMO MSC 428 compliance gap analysis
- Integration of cyber-risk management in the ISM
- Ensuring conformity with time-charter and insurances requirements
Cybersecurity by Design
- Design of vessel IT infrastructure
- Review of vessel IT/OT plans
- Systems integration management
- Implementation onsite
- Commissioning
- Project management

Training & Induction
- Cyber risk awareness induction
- Cyber risk protection and management training
- IT/OT shipboard systems vulnerabilities review and potential consequences of cyber attacks









